Every time you download an app especially outside the official store you are taking a risk. Performing a proper app authenticity check before installation can be the difference between protecting your data and handing it directly to a cybercriminal. Whether you are using Android, iOS, Windows, or macOS, verifying that an app is genuine, unmodified, and safe is no longer optional it is essential.
What Is an App Authenticity Check?
An app authenticity check is the process of verifying that a downloaded application is original, unmodified, and published by its legitimate developer. It confirms that no one has tampered with the package between the developer’s release and your device.
This includes checking:
- Digital signatures and code signing certificates
- SHA-256 or MD5 hash values (checksum verification)
- Publisher identity and certificate details
- App behavior through sandbox or antivirus scanning
Why App Authenticity Matters More Than Ever in 2026
Fake apps and tampered APKs are one of the fastest-growing cybersecurity threats globally. Attackers repackage legitimate apps injecting spyware, trojans, or adware and distribute them through unofficial channels.
Who is most at risk?
- Android users in Asia, Africa, and South America who sideload APKs from third-party sources
- Windows users downloading software outside the Microsoft Store
- Enterprise employees installing unauthorized business tools
- Developers who source libraries or plugins from unverified repositories
Organizations operating under GDPR (EU), CCPA (US), or PDPA (Asia) have compliance obligations that require app integrity verification before enterprise deployment.
Red Flags: Signs Your App May Be Fake or Tampered
Before going into verification methods, know what to watch for:
- App requests permissions that make no sense (a calculator asking for contacts)
- Publisher name is slightly misspelled (e.g., “Gooogle” or “WhatsAp”)
- File size is unusually large or small compared to the official version
- No reviews or suspiciously generic reviews
- App is not listed on the official developer’s website
- Certificate issuer is unknown or untrusted
If any of these apply, do not install the app until you have verified it.
How to Check App Authenticity on Android
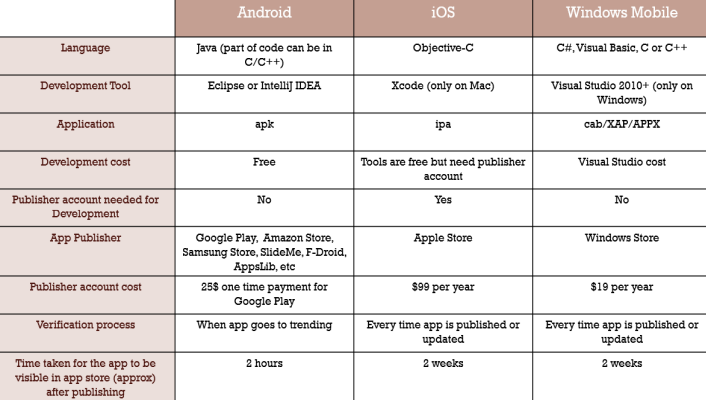
Android is the most targeted platform for fake apps due to widespread APK sideloading. Here is how to verify before installing.
Download only from trusted sources Use the official Google Play Store or the developer’s verified website. Before sideloading, always understand the core difference: APK vs Play Store What You Should Know
Check the APK digital signature Use APK Analyzer (built into Android Studio) or Jadx to inspect the signing certificate. The certificate CN (Common Name) should match the official developer. For a deeper understanding, read: Android App Signing Explained
Verify the SHA-256 hash Compare the file’s hash with the one published on the developer’s official page:
Windows: certutil -hashfile yourapp.apk SHA256
Linux/Mac: sha256sum yourapp.apkScan with VirusTotal Upload the APK to VirusTotal it runs the file through 70+ antivirus engines instantly and is the most trusted free tool for this purpose.
Enable Google Play Protect Go to Play Store → Menu → Play Protect. According to Google’s official support page, Play Protect scans billions of apps daily to keep Android devices safe.
Use APKSharp’s secure scanning guidance Before sideloading any APK, check: Secure APK Scanning Services
Also useful before sideloading:
- How to Install APK on Android Without Play Store
- Install Unknown Apps on Android
- Why APK File Not Installing on Android
How to Check App Authenticity on iOS
iOS has a more locked-down ecosystem, but risks still exist especially with enterprise certificates or TestFlight builds. Apple’s App Store Review Guidelines exist specifically to prevent tampered or malicious apps from reaching users.
Step 1 — Only install from the App Store Apple’s App Store review process is strict. Avoid third-party iOS app installers entirely.
Step 2 — Check developer information On the App Store page, tap the developer name. Verify it leads to a real company profile with other published apps.
Step 3 — Verify enterprise certificates Go to: Settings → General → VPN & Device Management. Any unknown certificate profile should be removed immediately.
Step 4 — Check app permissions post-install Go to Settings → Privacy & Security. Review what the app has access to and revoke anything unnecessary.
How to Check App Authenticity on Windows
Windows users often download software from third-party sites. Microsoft Authenticode is Microsoft’s official code signing standard that verifies publisher identity for every installer.
Step 1 — Check the digital signature Right-click the .exe or .msi file → Properties → Digital Signatures tab. Verify the signer name matches the official publisher.
Step 2 — Verify certificate details Click on the signature → Details → View Certificate. Confirm it is issued by a trusted Certificate Authority (CA) under the X.509 standard.
Step 3 — Check SHA-256 hash
certutil -hashfile setup.exe SHA256Compare with the hash published on the official download page. The NIST Digital Signature Standard defines why this matters for software integrity.
Step 4 — Scan with Windows Defender or VirusTotal Before running any installer, scan it on VirusTotal for a comprehensive multi-engine result.
How to Check App Authenticity on macOS
Step 1 — Use Gatekeeper macOS automatically checks apps against Apple’s notarization database. If an app is not notarized, macOS will warn you before it runs.
Step 2 — Verify code signature via Terminal
codesign -v --verbose /Applications/AppName.appA valid signature returns no errors.
Step 3 — Check notarization
spctl --assess --verbose /Applications/AppName.appOutput should say: “source=Notarized Developer ID”
Tool Comparison: Best Free Tools to Verify App Authenticity
| Tool | Platform | What It Does | Cost |
|---|---|---|---|
| VirusTotal | All | Multi-engine malware scan | Free |
| APK Analyzer | Android | Signature & manifest check | Free |
| Jadx | Android | Decompile & inspect APK | Free |
| Apktool | Android | Reverse engineer APK | Free |
| Authenticode | Windows | Code signing verification | Built-in |
| Codesign | macOS | Verify app signature | Built-in |
| Google Play Protect | Android | Real-time app scanning | Free |
Checksum Verification: The Most Reliable Method
A checksum is a unique fingerprint of a file generated using algorithms like SHA-256 or MD5. If even one byte of a file is changed, the checksum changes completely making this method impossible to fake.
How to use checksum verification:
- Go to the official developer’s website
- Find the published SHA-256 hash for the download
- Download the file
- Generate the hash on your device using the commands above
- Compare both hashes character by character they must match exactly
For a full technical breakdown of how app packages work before verifying them, read: What is an App Package File and Android App Signing Explained
Enterprise App Authenticity: B2B Considerations
For businesses deploying apps across teams, verification is not optional it is a compliance requirement. The OWASP Mobile Application Security Verification Standard (MASVS) provides a complete framework that enterprise security teams should follow.
Enterprise checklist:
- All apps must be signed with valid X.509 certificates
- APK or installer hashes must be logged before deployment
- Mobile Device Management (MDM) solutions should enforce app whitelisting
- App stores used must comply with GDPR, CCPA, or PDPA depending on region
- Security teams should perform sandbox testing of any new third-party tool
Sideloading: When Is It Safe?
Sideloading means installing an app outside the official store. It is common in regions where apps are geo-restricted. Before sideloading, always read about the real security threats involved: Security Threats When Installing Unofficial Apps
Also relevant: App is Not Available in Your Country and APK Downloader for Android Apps
Sideloading is relatively safer when:
- The APK is downloaded from the developer’s own official website
- Hash is verified before installation
- The file is scanned on VirusTotal with clean results
- You understand the permissions being granted
Sideloading is dangerous when:
- Downloaded from random forums, Telegram groups, or unknown mirror sites
- No hash or certificate information is available
- The app requests excessive permissions
For special file formats, also check: Install XAPK Files on Android and How to Install APK on PC Using an Emulator
Common Mistakes People Make
- Skipping hash verification because “it looks official”
- Trusting app icons and screenshots as proof of authenticity
- Installing APKs from Telegram or WhatsApp groups
- Ignoring certificate warnings during installation
- Not updating apps outdated versions may contain known vulnerabilities
Related: How to Update APK Without Losing Data and How to Back Up Android App Data
Quick Verification Checklist
- Downloaded from official source or trusted mirror
- SHA-256 hash matches official published value
- Digital signature certificate is valid and trusted
- Publisher name is verified and correct
- Scanned clean on VirusTotal
- App permissions are appropriate for its function
- Google Play Protect or equivalent is enabled
- No unusual behavior after install (battery drain, data usage spike)
FAQs
Q1: How do I know if an app is legitimate?
Check if it is published in an official store, verify the developer’s certificate, compare the SHA-256 hash with the value on the official site, and scan it with VirusTotal before installing.
Q2: Can fake apps steal your data?
Yes. Fake apps often contain spyware or trojans that silently harvest passwords, banking credentials, contacts, and location data without any visible sign on your device.
Q3: What is checksum verification and why does it matter?
Checksum verification generates a unique hash for a file using SHA-256 or MD5. If the file has been modified in any way, the hash will not match the official value immediately exposing it as tampered.
Q4: Is sideloading apps safe?
Only if you verify the hash, confirm the digital signature, and scan with VirusTotal first. Sideloading from unverified sources without these steps is a serious and avoidable security risk.
Conclusion
An app authenticity check is not a technical luxury it is a basic security habit every user and organization should build. Whether you are installing an APK on Android, a DMG on macOS, or an EXE on Windows, taking five minutes to verify the digital signature, compare the checksum, and scan with VirusTotal can save you from data theft, malware infection, or compliance violations.
Start with official sources. Verify before you trust. And when in doubt do not install.